Windows Firewall allows to restrict inbound/outbound network traffic for a certain application, protocol or a TCP/IP port. This is an easy way to restrict network access to/from user workstations or servers. You can configure Windows Firewall rules individually on each computer or, if a user computer is joined to an Active Directory domain, an administrator can manage Windows Defender Firewall settings and rules using GPO.
In large enterprises, the port filtering rules are usually set at the level of routers, L3 switches or dedicated firewall devices. However, nothing prevents you from deploying your Windows Firewall network access restriction rules to workstations or Windows servers.
Group Policy Settings to Manage Windows Defender Firewall Rules
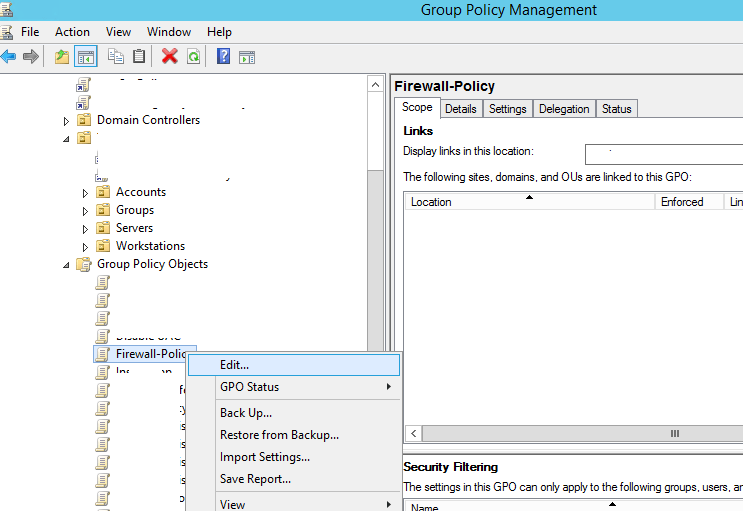
Using the domain group policy editor (Group Policy Management console – gpmc.msc), create a new GPO object (policy) with the name Firewall-Policy and switch to the edit mode.
There are two sections in the Group Policy Management console that allow you to manage firewall settings:
- Computer Configuration -> Administrative Templates -> Network -> Network Connections -> Windows Firewall – this GPO section was used to configure firewall rules in OS Vista/Windows Server 2008 or earlier. If you don’t have any computers with these old OS versions, use the next policy section to configure your firewall;
- Computer Configuration -> Windows Settings -> Security Settings -> Windows Firewall with Advanced Security – is the actual section to configure Windows Firewall in modern Windows OS versions, and its interface is similar to that of the local Defender Firewall management console.
How to Enable Windows Firewall Using GPO?
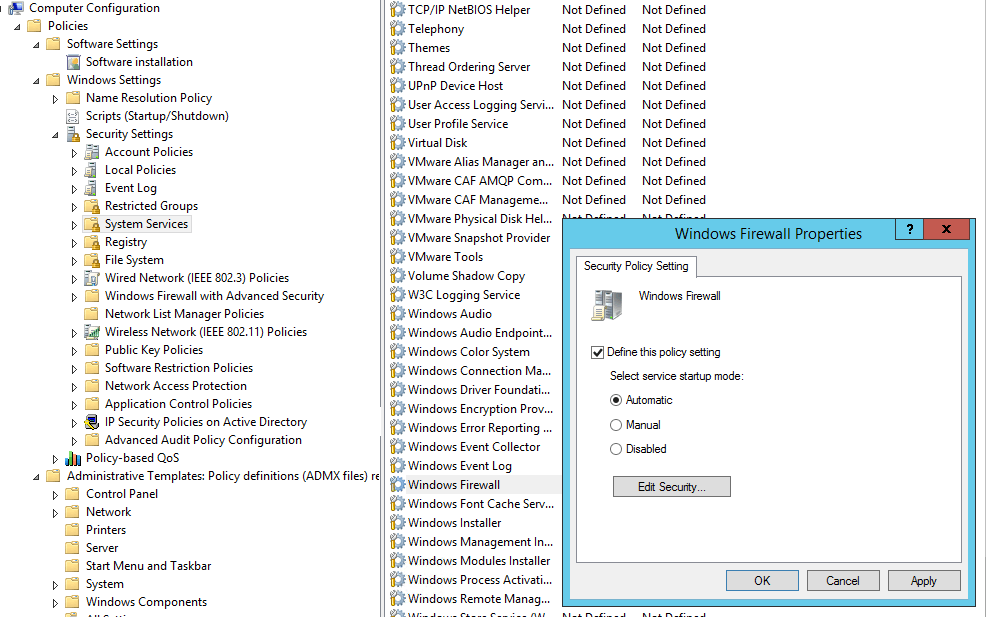
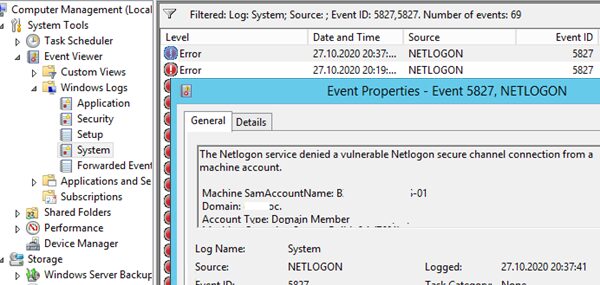
In order users (even having local admin permissions) cannot stop the firewall service, it is recommended to configure the automatic startup of Windows Firewall using GPO. To do it, go to Computer Configuration- > Windows Settings -> Security Settings -> System Services. Find Windows Firewall in the list of services and change the startup mode to automatic (Define this policy setting -> Service startup mode Automatic). Make sure that your users don’t have the permissions to stop the service.
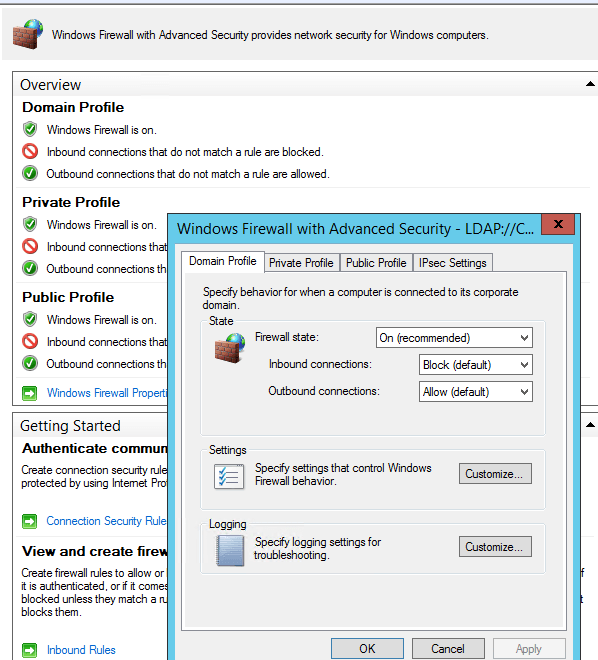
Go to the Computer Configuration -> Windows Settings -> Security Settings section in the GPO console. Right-click Windows Firewall with Advanced Security and open the properties.
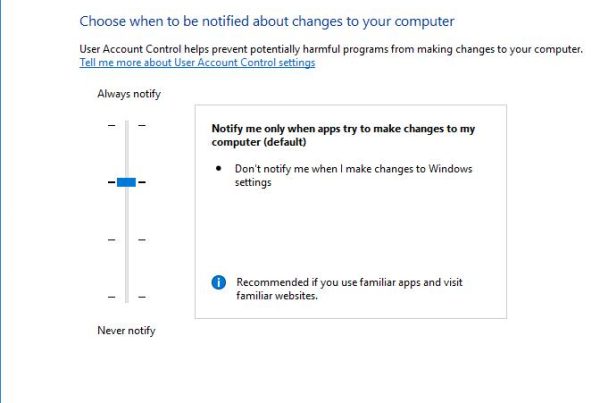
Change the Firewall state to On (recommended) in all three tabs: Domain Profile, Private Profile and Public Profile. Depending on the security policies in your company, you can specify that all inbound connections are blocked by default (Inbound connections -> Block), and outbound connections are allowed (Outbound connections -> Allow). Save the changes.
How to Create a Firewall Rule Using GPO?
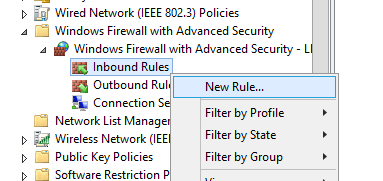
Let’s try to create an allowing inbound Windows Firewall rule. For example, we want to allow the incoming RDP connection to all computers (TCP 3389 port). Right-click the Inbound Rules section and select New Rule.
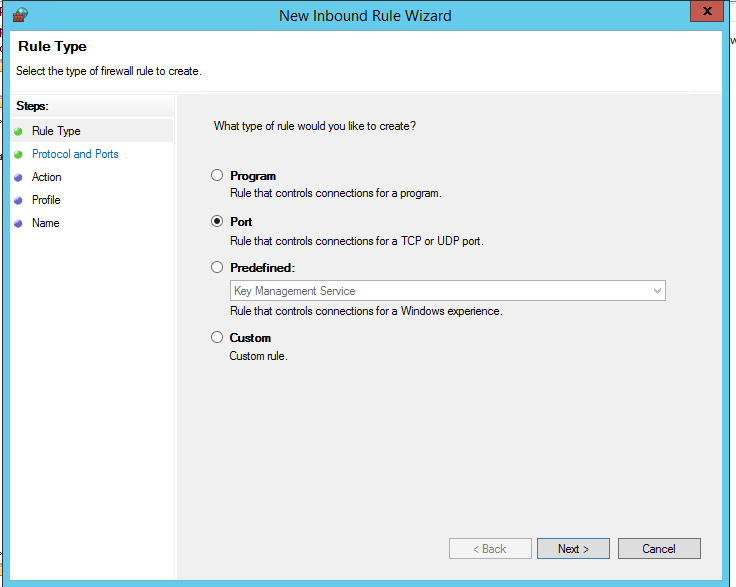
The firewall rule wizard has an interface similar to that of local Windows Firewall on the user’s desktop computer.
Select the rule type. You can allow access to:
- Program – you can select a program executable (.exe);
- Port – you can select a TCP/UDP port or a port range;
- Predefined – you can select one of the standard Windows rules, which already contain access rules (both executable files and ports are described) to typical services (e. g., AD, HTTP(s), DFS, BranchCache, remote restart, SNMP, KMS, etc.);
- Custom – here you can specify a program, a protocol (protocols other than TCP or UDP, like ICMP, GRE, L2TP, IGMP, etc.), client IP addresses or entire IP subnets.
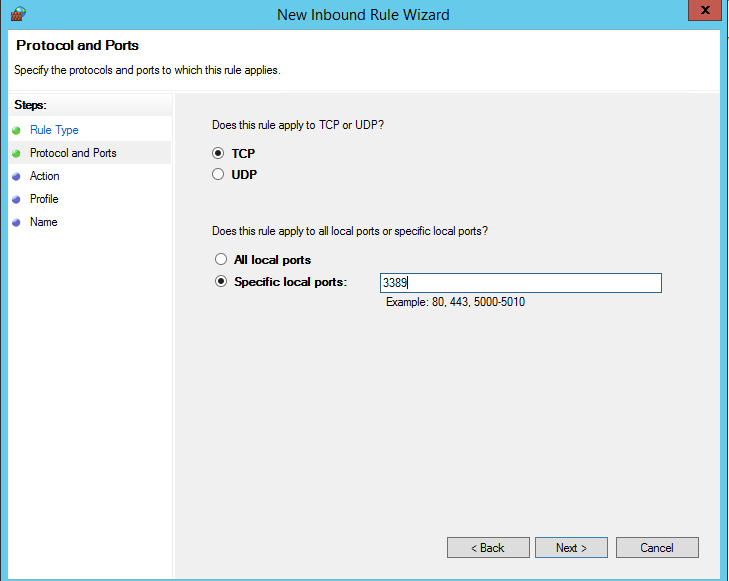
In our case, we’ll select the Port rule. Let’s specify TCP as the protocol, and Port 3389 as the port (it is the default RDP port, but you can change it via the registry).
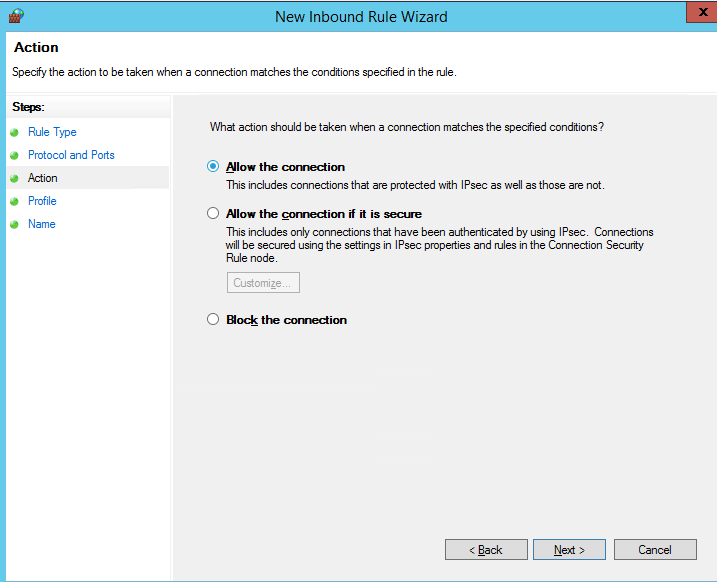
Then you must select what to do with such a network connection: Allow the connection, allow if it is secure or Block the connection.
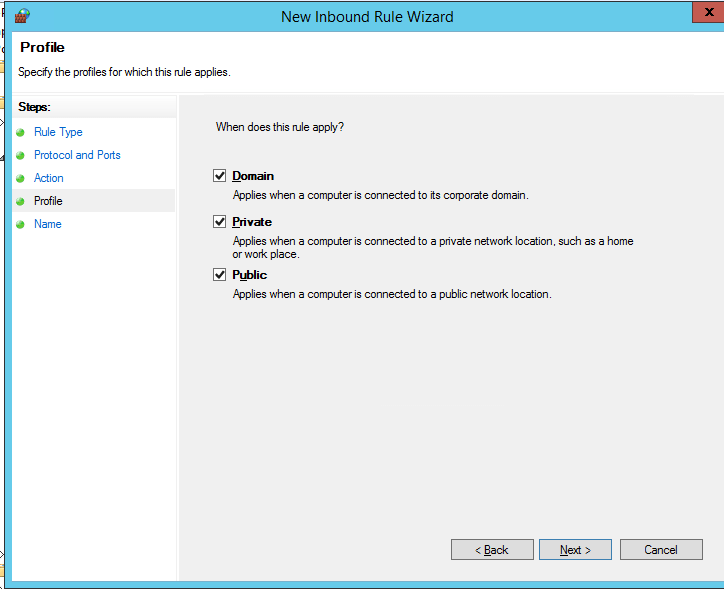
Then select the firewall profiles to apply the rule to. You can leave all profiles enabled (Domain, Private and Public).
On the last step, specify the name and description of the rule. Click Finish, and it will appear in the list of firewall rules.
In the same way you can configure other rules for the inbound traffic to be applied to your Windows clients.Don’t forget to create rules for the inbound and outbound traffic.
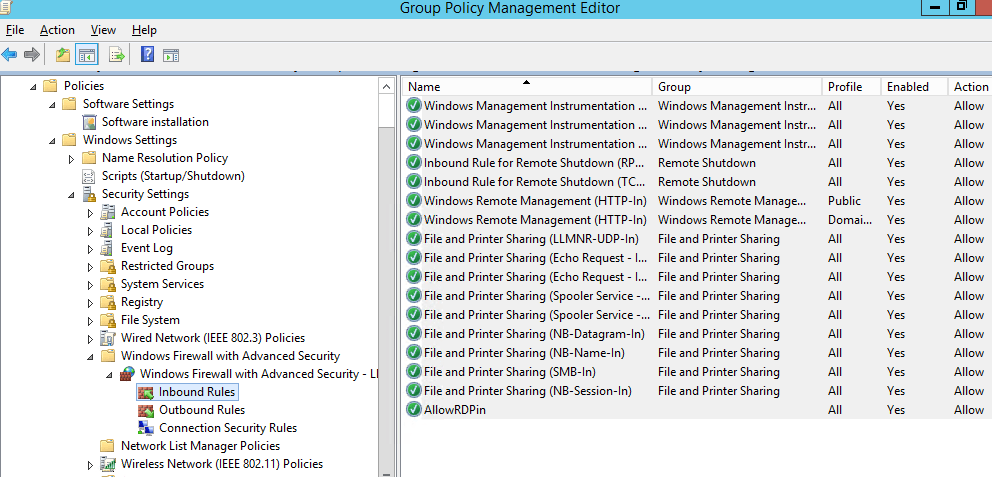
Now just assign the Firewall Policy to the OU with user computers.
Important – Before applying the firewall policy to OU with productive computers, it is strongly recommend to try it out on some test computers. Otherwise, due to wrong firewall settings, you can paralyze you enterprise network. To diagnose how your group policy is applied, use the gpresult tool.
Testing Windows Firewall Policies on Clients
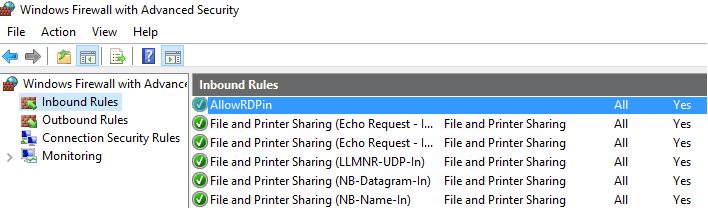
Update the group policy settings on your clients (gpupdate /force). Make sure that the ports you have specified are available on user computers (you can use Test-NetConnection cmdlet or Portqry tool).
On a user PC, open the Control Panel -> System&Security -> Windows Defender Firewall and make sure that there is the message For your security, some settings are controlled by Group Policy and your firewall settings are used.
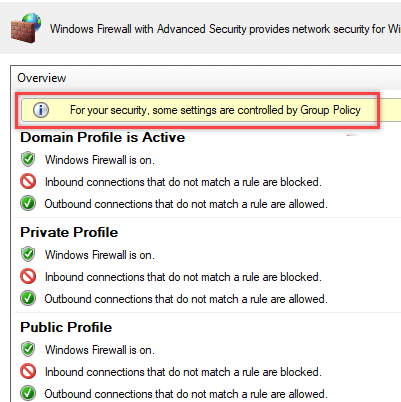
Now a user cannot change firewall settings, and all rules that you have created must appear in the Inbound Rules list.
You can also display the firewall settings using this command:
netsh firewall show state
How to Import/Export Windows Firewall Rules to/from GPO?
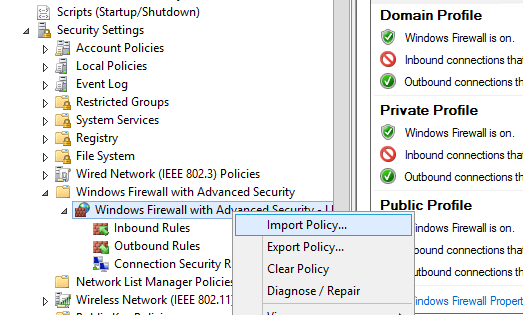
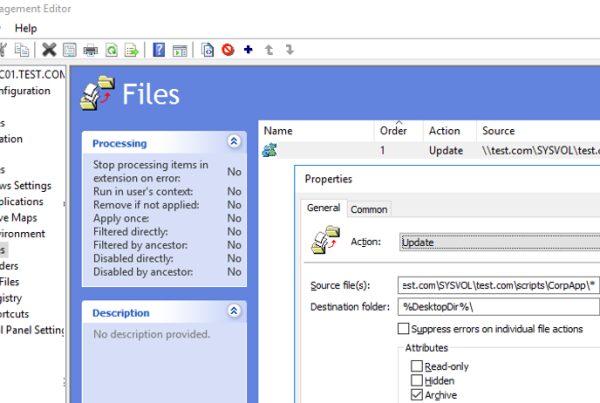
Of course, the process of creating Windows Firewall rules is a painstaking and time consuming task (however, it is worth the effort). To make it easier, you can import/export Windows Firewall settings. To do it, it’s enough to configure local firewall settings on a reference workstation as you need. Then go to the root of Windows Firewall snap-in (Windows Firewall with Advanced Security) and select Action -> Export Policy.
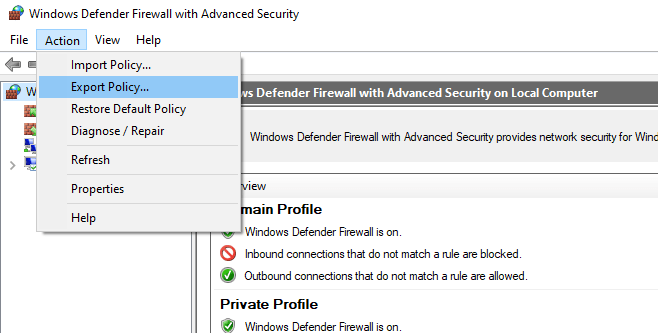
The policy will be exported into a WFW file, which can be imported to the Group Policy Management Editor by selecting Import Policy option and specifying the path to the .wfw file (the current policy settings will be overwritten).
Domain and Local Windows Defender Firewall Rules
Depending on whether you want that local administrators can create their own firewall rules on their computers to be combined with the rules obtained from the group policy, you can select the rule merging option. Open the policy properties and view the settings in the Rule merging section. By default rule merging is enabled. You can force that a local administrator can create their own firewall rules: select Yes (default) in the Apply local firewall rules option.
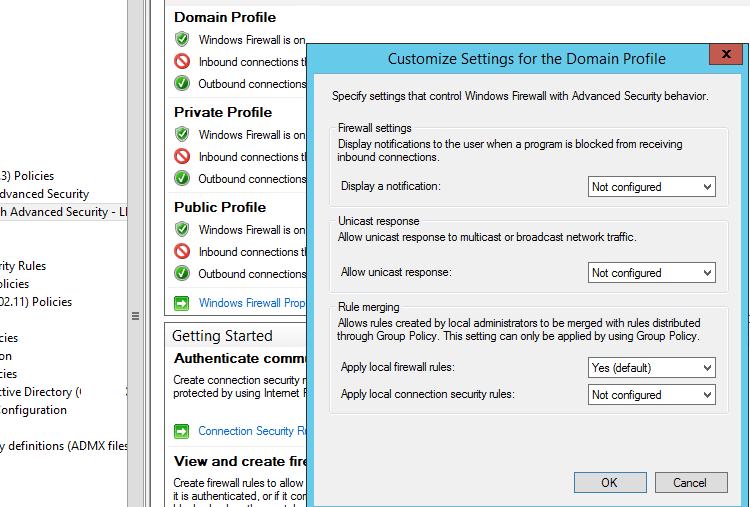
Tip – Blocking firewall rules have higher priority than the allowing ones. It means that a user cannot create an allowing access rule if it contradicts the blocking rule configured by an administrator using GPO. However, a user will be able to create a local blocking rule, even if the access is allowed in the policy by the administrator.
Tips: Managing Windows Firewall with GPOs
Of course, you should create separate policies to manage Windows Firewall rules for servers and workstations (you may have to create separate policies for each group of similar servers depending on their role). It means that firewall rules for the domain controller, an Exchange mail server and an SQL server will differ.
You can find what ports must be opened for each service on the vendor’s website. The process is quite painstaking and complicated at the first glance. However, you can finally get a working Windows Firewall configuration that allows only approved network connections and blocks other ones. From my experience, I’d like to note that you can quickly find the list of used TCP/UDP ports for Microsoft software.
Nice article.
Does Disabling the Rule Merging also mean that Applications that get installed can’t create a local allow rule on a workstation? Would a GPO based allow rule be required and targeted for machines with that application?
Jarret
They aren’t prevented from creating the rule, however GPO rules will always take precedence, So while an app can create a rule for say TCP/4444 as an example, if you have targeted a GPO here and disabled rule merging that rule of tcp/4444 won’t work, in this example you will also have to add the same rule to the GPO to get it to work.